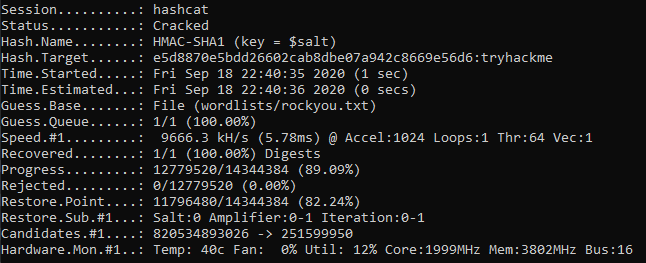
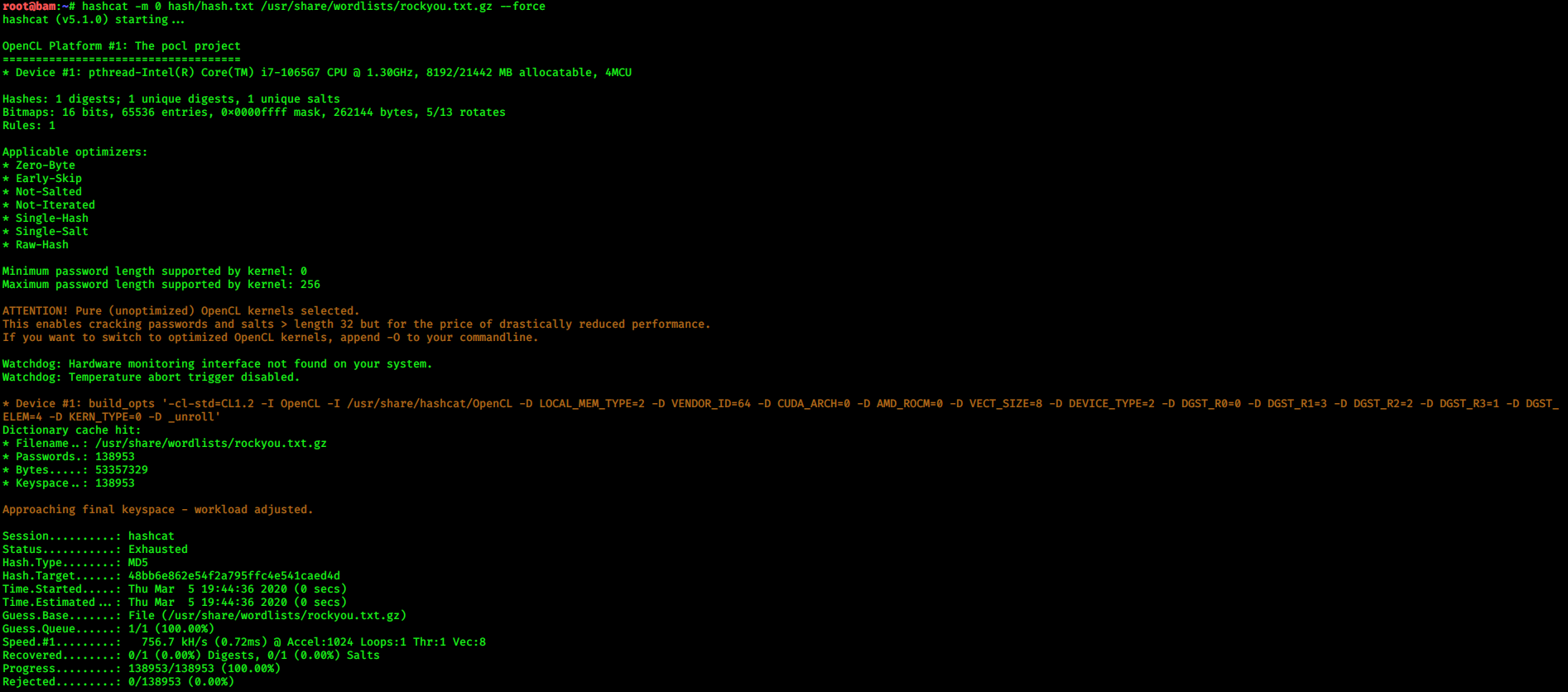
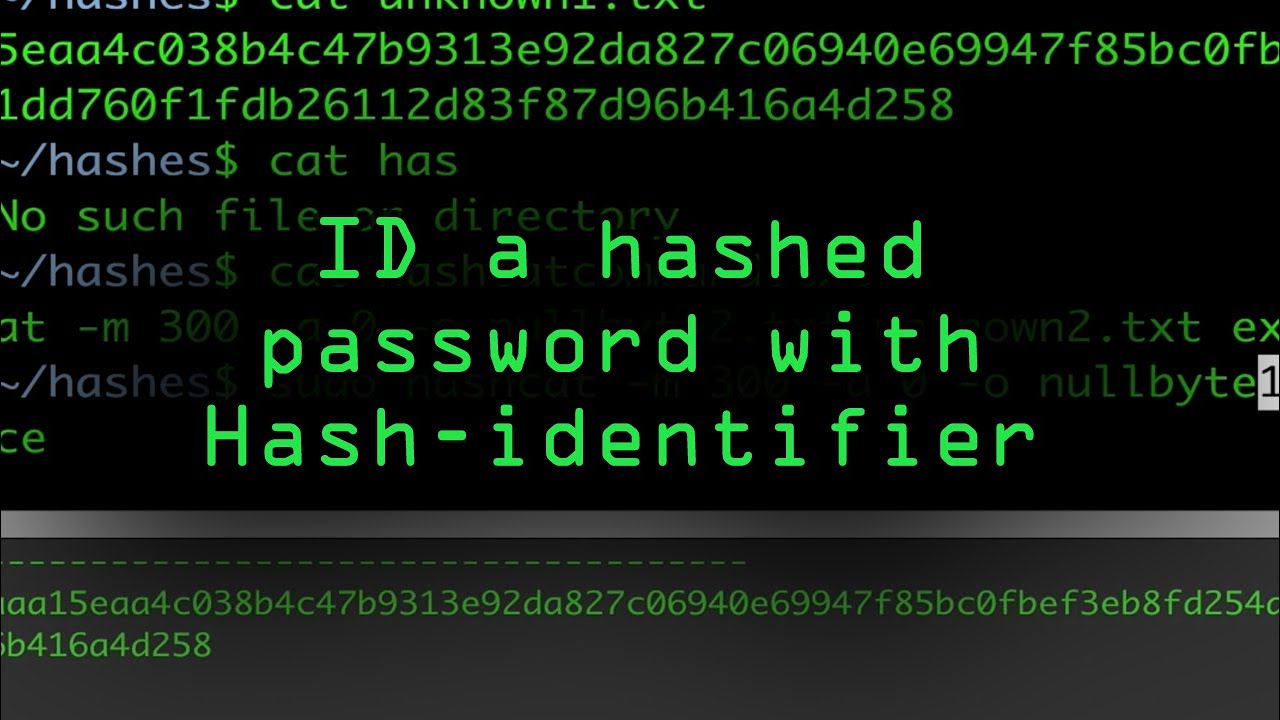
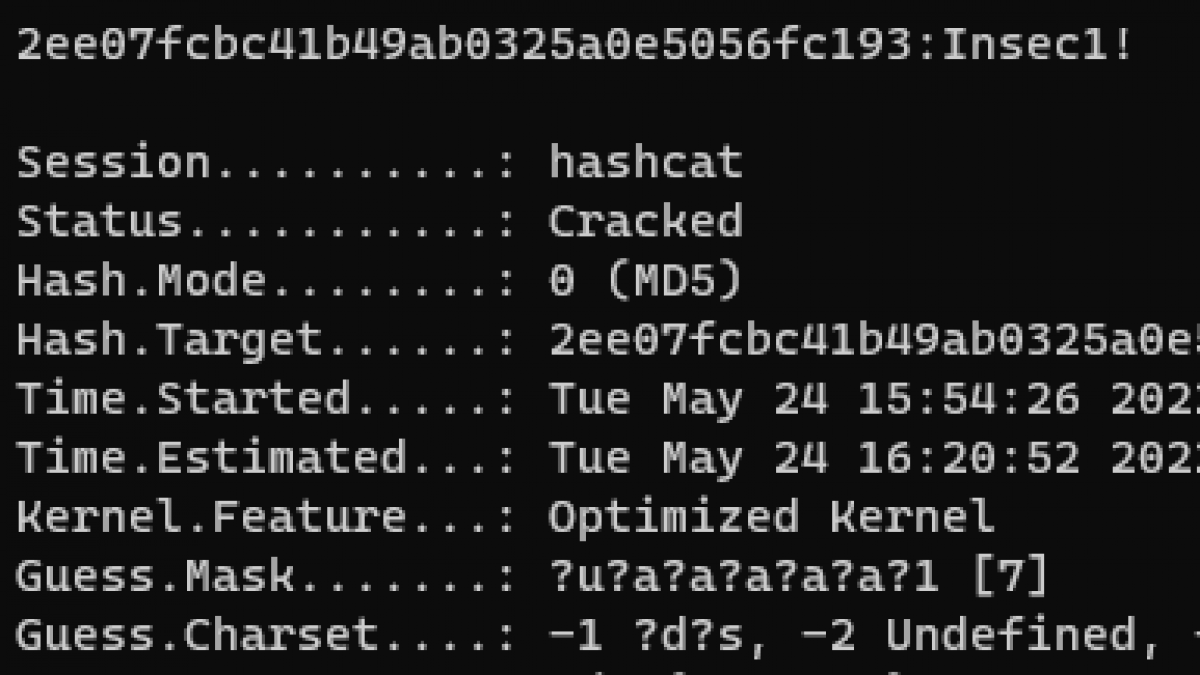
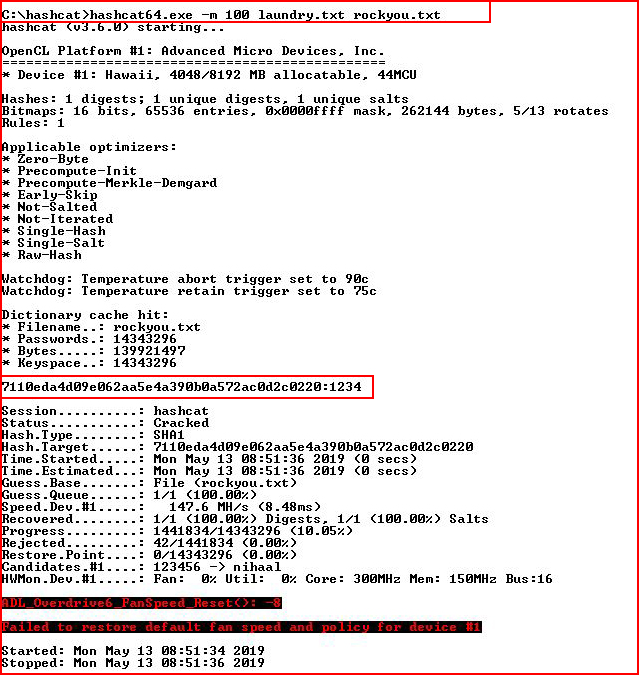
Identifying and Cracking Hashes. During a penetration test or a simple… | by Mr. Robot | InfoSec Adventures | Medium

How to identify hash types – new tools with modern hashes support - Ethical hacking and penetration testing

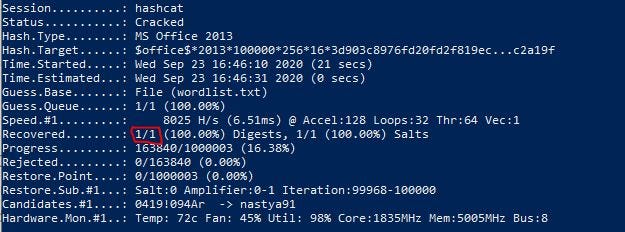
Challenge Description A hacker leaked the below hash online.Can you crack it to know the password of the CEO? the flag is the password Hash:06f8aa28b9237866e3e289f18ade19e1736d809d First go to hash… - arnold sydney -


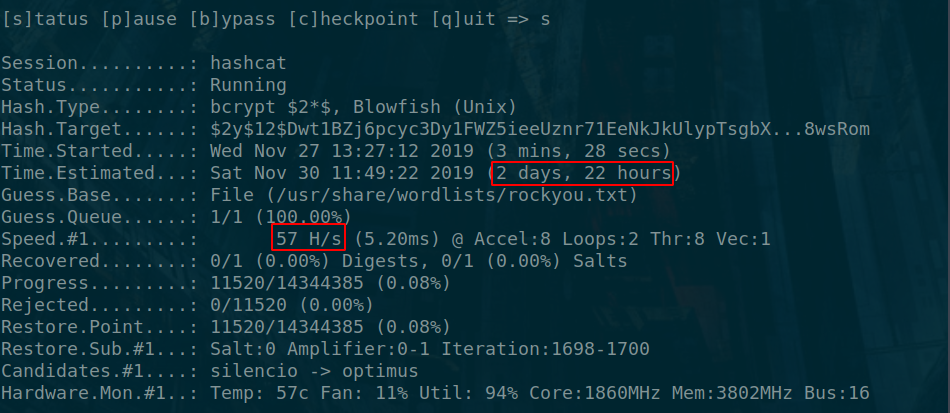


![Hashcat tutorial for beginners [updated 2021] | Infosec Resources Hashcat tutorial for beginners [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2018/04/122120-2.png)





![hashcat [hashcat wiki] hashcat [hashcat wiki]](https://hashcat.net/wiki/lib/exe/fetch.php?tok=505d08&media=https%3A%2F%2Fhashcat.net%2Fhashcat%2Fhashcat.png)